On 8 May 2025 at approximately 05:49 BST, theEverest Ransomware Grouppurportedly claimed responsibility for a cyber‐intrusion against Kaefer, one of the world’s leading industrial insulation and access specialists. According to the group’s online communiqué, stolen materials include internal correspondence, project documentation and support tickets drawn directly from Kaefer’s Freshdesk customer-service platform.
Careful examination of the screenshots released by Everest suggests the authenticity of the breach. The images appear to be genuine captures of the Freshdesk interface, complete with ticket identifiers, timestamps and user‐level permission indicators. While the precise volume of exfiltrated data remains unclear, initial signs point towards the compromise of sensitive operational records, potentially exposing client names, case histories and internal service‐level agreements.
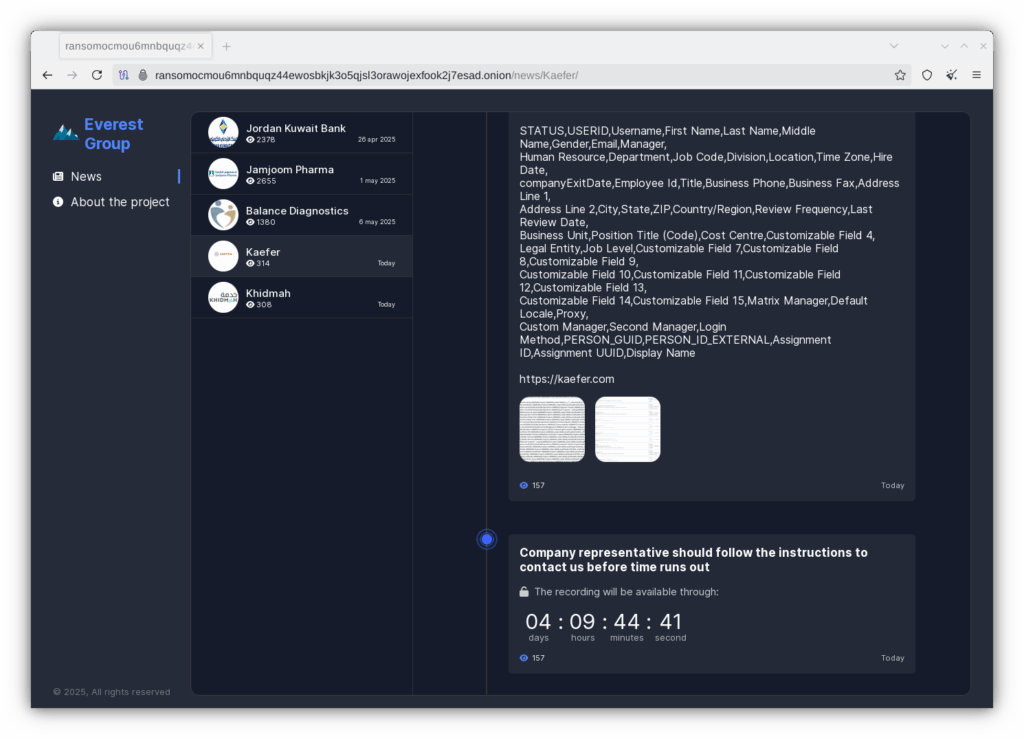
Everest’s modus operandi typically involves encrypting critical data and demanding payment in cryptocurrency, coupled with the threat to publish or sell stolen files if their ransom demands are not met. In this instance, however, the group has already demonstrated a willingness to publicise the breach, placing additional pressure on Kaefer’s incident-response team to contain the fallout and reassure affected stakeholders.
Kaefer’s security operations centre (SOC) has not yet issued a formal statement, and it remains to be seen whether the organisation will confirm the incident or disclose the scope of any ransomware encryption. Equally, there is no indication at present that Kaefer has acceded to the attackers’ demands. In the absence of an official response, independent cyber-security analysts are scouring the dark web and known ransomware forums for corroborating evidence of stolen datasets.
Should further details emerge—whether regarding the nature of the exfiltrated data, the ransom note itself, or Kaefer’s mitigation measures—we shall report them without delay. In the interim, organisations that use Freshdesk or similar cloud-based ticketing systems would be prudent to review their access logs, enforce multifactor authentication and ensure that all endpoint protection platforms are fully updated. Vigilance and rapid response remain the best defences against ransomware actors such as the Everest Group.
What would be recommend
Implementing robust two-factor authentication (2FA) within Freshdesk can significantly strengthen your organisation’s defences by introducing an additional barrier against unauthorised access. First and foremost, ensure that 2FA is enabled not only for all administrative and agent accounts, but—where possible—for end-user (customer) logins as well. Under the Security settings in your Freshdesk admin console, activate Time-based One-Time Password (TOTP) authentication and mandate its use for every user. By making 2FA compulsory, you eliminate the possibility of weaker or reused passwords serving as a single point of failure, and you align your helpdesk platform with best-practice access controls.
When selecting a second factor, favour authenticator apps such as Google Authenticator, Microsoft Authenticator or FreeOTP over SMS or email‐based codes. Authenticator applications generate one-time codes directly on the user’s device, reducing the risk of interception via SIM-swap or phishing attacks. Freshdesk’s TOTP option integrates seamlessly with these apps, and you should configure the system to issue backup or emergency recovery codes that agents must securely store. These printed or digitally archived codes ensure continuity of access should a device be lost or replaced, while still preserving the integrity of the 2FA process.
If your organisation leverages single sign-on (SSO) via SAML or OAuth providers, it is prudent to delegate Freshdesk authentication to an identity provider that already enforces multi-factor policies. By federating authentication through Azure Active Directory, Okta or another enterprise identity service, you can centralise control of security settings—including 2FA complexity, conditional access and device compliance—thereby unifying governance across all cloud applications. This approach not only simplifies the user experience but also ensures that any enhancements or policy changes made at the identity-provider tier automatically extend to Freshdesk.
Beyond technical implementation, cultivate a security-first culture by communicating clearly with your team about the importance of 2FA and providing step-by-step guidance on setting it up. Conduct periodic audits of Freshdesk’s access logs to identify login attempts that bypass or fail 2FA challenges, and escalate any suspicious activity for immediate investigation. Finally, couple your 2FA measures with complementary controls—such as role-based permissions, regular password rotation and up-to-date endpoint protection—to create a layered defence that deters ransomware threat actors and other malicious intruders from exploiting your customer-support infrastructure.



Stay Informed. Stay Secure.